Article Plan: “A Mind Spread Out on the Ground” PDF

This article explores Leanne Betasamosake Simpson’s impactful work, examining themes of colonialism, trauma, and racism, alongside its reception and contemporary relevance․
BOOKEY offers summaries, while the text itself, available as a PDF, demands patience and a deep engagement with challenging subject matter․
The plan details the book’s structure, key concepts like Nishnaabeg worldview, and the intersection of colonialism with mental health, referencing Hemer’s (2018) work․
Leanne Betasamosake Simpson’s “A Mind Spread Out on the Ground” is a profoundly impactful work, quickly establishing itself as a national bestseller in Canada and gaining recognition within the United States․ This book isn’t a conventional narrative; it’s described as a bold meditation on deeply challenging themes – trauma, the enduring legacy of colonialism, systemic oppression, and the pervasive nature of racism in North America․
Readers should prepare for a demanding, yet rewarding, experience․ The writing style is unique, often described as creative and requiring patience․ Accessing the text as a PDF allows for focused study, though resources like BOOKEY offer summaries for those seeking a quicker overview․ The book’s power lies in its unflinching examination of difficult truths, prompting introspection and a deeper understanding of Indigenous experiences․
It’s a work that invites contemplation, encouraging readers to navigate complex ideas surrounding historical injustices and their ongoing consequences․
Author Biography: Leanne Betasamosake Simpson
Leanne Betasamosake Simpson is an award-winning Michi Saagiig Nishnaabeg scholar, writer, and artist․ Her multifaceted work spans poetry, fiction, essays, and traditional Anishinaabe teachings․ She holds a Ph․D․ from the University of Western Ontario and is widely recognized for her commitment to Indigenous knowledge and decolonial thought․
Simpson’s writing consistently centers Indigenous perspectives, challenging dominant narratives and advocating for social justice․ “A Mind Spread Out on the Ground” exemplifies her dedication to exploring the complexities of Indigenous trauma, resilience, and the ongoing impacts of colonialism․ Her work isn’t simply academic; it’s deeply rooted in lived experience and community engagement․

She is a vital voice in contemporary literature, and her book, available as a PDF, reflects her profound understanding of history, culture, and the urgent need for reconciliation․ Resources like BOOKEY can offer introductory insights into her broader body of work․
Core Themes of the Book
“A Mind Spread Out on the Ground” profoundly explores the interconnected themes of legacy, oppression, and racism within North America․ The book serves as a bold meditation on trauma, examining its intergenerational effects on Indigenous communities․ It doesn’t shy away from confronting the harsh realities of colonial violence and its lasting consequences․

Central to the work is an investigation into how historical injustices continue to shape present-day experiences․ The PDF version allows for close reading of Simpson’s nuanced arguments․ The text requires patience, but rewards readers with a deeper understanding of these complex issues․
Furthermore, the book delves into the psychological and emotional toll of systemic discrimination, offering a powerful critique of societal structures․ BOOKEY summaries can provide a starting point, but the full text offers a richer, more immersive experience․
Colonialism and its Impact
“A Mind Spread Out on the Ground,” available as a PDF, meticulously dissects the pervasive impact of colonialism on Indigenous peoples․ The book doesn’t present colonialism as a distant historical event, but as a continuing force shaping contemporary realities․ It highlights how colonial structures have systematically dismantled Indigenous ways of life, fostering trauma and dispossession․
Simpson’s work reveals how colonialism has exacerbated mental health issues within Indigenous communities, a crucial point explored in dedicated chapters․ The text demonstrates a clear link between historical oppression and present-day struggles․

The book’s exploration extends to the insidious justifications for colonial violence, even referencing Thomas Jefferson’s adoption of genocidal rationales․ BOOKEY can offer a brief overview, but the PDF provides the full weight of Simpson’s analysis․
Indigenous Trauma and Healing
“A Mind Spread Out on the Ground,” in its complete PDF form, offers a profound meditation on intergenerational trauma within Indigenous communities․ Simpson doesn’t shy away from the painful realities of oppression and racism, acknowledging their lasting psychological and emotional scars․
However, the book is not solely focused on trauma; it also explores pathways toward healing․ While acknowledging the depth of the wounds, Simpson subtly weaves in elements of resilience and the enduring strength of Indigenous knowledge systems․
The text suggests that true healing requires a reckoning with the past and a commitment to dismantling colonial structures․ BOOKEY summaries may touch upon this, but the PDF allows for a nuanced understanding of Simpson’s complex approach to trauma and recovery․
Legacy of Oppression and Racism
“A Mind Spread Out on the Ground,” as experienced through the complete PDF version, powerfully illustrates the enduring legacy of oppression and systemic racism in North America․ The book doesn’t present these as historical events, but as ongoing forces shaping contemporary Indigenous experiences․
Simpson meticulously details how colonial policies and attitudes continue to manifest in various forms of social injustice, impacting mental health, community well-being, and cultural survival․ The text reveals a disturbing pattern of justification for harmful actions, even reaching figures like Thomas Jefferson․
Exploring specific chapters reveals how these legacies are deeply embedded within family histories and collective memory․ While BOOKEY might offer a condensed overview, the PDF provides the necessary depth to fully grasp the scope of this historical and present-day reality․
The Book’s Structure and Style
“A Mind Spread Out on the Ground,” in its complete PDF form, defies conventional narrative structures․ It’s not a linear story, but rather a collection of fragmented thoughts, poems, and essays, mirroring the fractured experience of trauma and displacement․
The style is deliberately non-traditional, employing a stream-of-consciousness approach that demands active engagement from the reader․ This stylistic choice isn’t accidental; it reflects a Nishnaabeg worldview that prioritizes relationality and interconnectedness over rigid categorization․
While apps like BOOKEY can provide summaries, they struggle to capture the nuance of Simpson’s prose․ The PDF allows for a slower, more contemplative reading, essential for appreciating the book’s poetic language and challenging form․ It’s a work of creativity, a masterpiece in its own right․
Key Concepts Explored in the Text
The “A Mind Spread Out on the Ground” PDF deeply explores foundational Indigenous concepts, central to understanding its powerful message․ Nishnaabeg worldview, emphasizing interconnectedness and the land, is paramount, shaping the book’s fragmented structure and poetic language․
Anishinaabe kinship systems, often overlooked in Western thought, are presented as vital for healing and resisting colonial structures․ The text challenges readers to reconsider traditional notions of family and community․
Understanding these concepts is crucial; summaries, even those offered by apps like BOOKEY, can’t fully convey their depth․ The PDF allows for a direct encounter with Simpson’s articulation of these ideas, revealing their profound implications for addressing trauma and oppression․
Nishnaabeg Worldview
The Nishnaabeg worldview, central to “A Mind Spread Out on the Ground” PDF, fundamentally differs from Western perspectives․ It emphasizes a deep, reciprocal relationship with the land, viewing all living things as interconnected and possessing inherent value․ This isn’t merely an environmental ethic, but a foundational principle shaping all aspects of life․
Simpson’s work embodies this worldview through its fragmented, non-linear structure, mirroring the cyclical nature of life and the interconnectedness of stories․ The PDF format allows readers to fully immerse themselves in this perspective, experiencing the text as a living entity rather than a static object․
Understanding this perspective is vital for interpreting the book’s exploration of trauma and healing, as it offers an alternative framework for understanding well-being beyond colonial definitions․
Anishinaabe Kinship Systems
“A Mind Spread Out on the Ground” PDF intricately portrays Anishinaabe kinship systems, extending beyond immediate family to encompass all living beings and the natural world․ These systems aren’t simply about biological relation, but about reciprocal responsibility and interconnectedness – a web of obligations and support;
The book demonstrates how colonial disruption of these kinship structures has profoundly impacted Indigenous communities, contributing to trauma and loss of identity․ Accessing the PDF allows for a deeper understanding of these complex relationships, presented not as abstract concepts, but as lived realities․
Simpson’s narrative highlights how restoring and revitalizing kinship is crucial for healing and resisting ongoing colonialism, offering a pathway towards collective well-being․
Intersection of Colonialism and Mental Health
“A Mind Spread Out on the Ground” PDF powerfully illustrates the devastating intersection of colonialism and Indigenous mental health․ The text reveals how colonial policies and ongoing systemic oppression have directly contributed to intergenerational trauma, grief, and increased rates of mental health challenges within Anishinaabe communities․

The book doesn’t present mental health issues as individual pathologies, but as logical responses to historical and ongoing violence․ Scanning to download reveals a nuanced exploration of this connection, emphasizing the need for culturally-informed healing approaches․
Understanding this intersection, as presented in the PDF, is vital for dismantling colonial structures and fostering genuine reconciliation․

The Role of Storytelling and Oral Tradition
“A Mind Spread Out on the Ground” PDF deeply values storytelling and oral tradition as central to Anishinaabe knowledge, healing, and resistance․ The book itself embodies this tradition, moving beyond linear narratives to embrace a more fluid, cyclical, and relational approach to conveying complex truths․
The text demonstrates how stories aren’t simply recounting events, but actively shaping reality and maintaining cultural continuity in the face of colonial disruption․ BOOKEY summaries may offer outlines, but cannot replicate the power of Simpson’s stylistic choices․
Accessing the PDF reveals a profound commitment to reclaiming and revitalizing Indigenous ways of knowing through the enduring power of narrative․
Analysis of Specific Chapters (Based on Available Information)
Analyzing “A Mind Spread Out on the Ground” PDF reveals chapters deeply engaged with the lasting impact of historical trauma and systemic oppression․ While detailed chapter breakdowns are limited in readily available information, the overall structure suggests a deliberate exploration of legacy and its manifestations․
The text confronts racism and its pervasive influence, likely through personal narratives and reflections on collective experiences․ BOOKEY apps can provide summaries, but lack the nuance of Simpson’s prose․
The book’s power lies in its ability to connect individual struggles to broader patterns of colonial violence, demanding a reckoning with uncomfortable truths․ The PDF format allows for close reading and deeper engagement with these complex themes․
Examination of Chapters Dealing with Legacy
Chapters focusing on legacy within “A Mind Spread Out on the Ground” PDF delve into the intergenerational transmission of trauma stemming from colonialism and historical injustices․ The book, a national bestseller, meticulously unpacks how past oppressions continue to shape present realities for Indigenous communities․
These sections likely explore the weight of ancestral experiences, the disruption of cultural practices, and the enduring effects of racism․ BOOKEY summaries offer a glimpse, but cannot fully capture the emotional depth and complexity of Simpson’s writing․
The examination of legacy isn’t simply about recounting the past; it’s about understanding how it actively informs identity, relationships, and the ongoing struggle for healing and self-determination․
Chapters Focusing on Oppression and Racism
Within “A Mind Spread Out on the Ground” PDF, chapters dedicated to oppression and racism confront the systemic injustices faced by Indigenous peoples in North America․ The text, described as a profound meditation, doesn’t shy away from detailing the historical and contemporary manifestations of these forces․
These sections likely dissect the ways in which colonial structures perpetuate inequality, marginalization, and violence․ BOOKEY app summaries can provide an overview, but the book’s nuanced exploration requires a direct engagement with Simpson’s prose․
The narrative likely examines the psychological and emotional toll of racism, alongside the resilience and resistance of Indigenous communities in the face of ongoing adversity․ It’s a challenging, yet crucial, examination of a painful history․
Reception and Critical Acclaim
“A Mind Spread Out on the Ground” PDF has garnered significant recognition, notably as a national bestseller in Canada․ This acclaim speaks to the book’s powerful resonance with readers and its importance in contemporary discourse․ Critics have lauded Simpson’s work as a bold and profound exploration of trauma, legacy, oppression, and racism․
The book’s impact extends beyond sales figures, sparking conversations about Indigenous experiences and the ongoing effects of colonialism․ BOOKEY app summaries highlight its accessibility, but the full depth of the work is best experienced through direct reading․
Its success demonstrates a growing appetite for Indigenous voices and perspectives, and a willingness to confront difficult truths about North American history and society․ The book’s enduring appeal solidifies its place as a significant literary achievement․
“A Mind Spread Out on the Ground” as a National Bestseller
Achieving national bestseller status in Canada, “A Mind Spread Out on the Ground” PDF signifies a remarkable reception for Leanne Betasamosake Simpson’s work․ This success isn’t merely a matter of sales; it represents a cultural moment, indicating a broad readership eager to engage with challenging narratives about colonialism and its lasting impacts․
The book’s popularity suggests a growing awareness and demand for Indigenous voices and perspectives within the literary landscape․ BOOKEY provides summaries, but the book’s bestseller status highlights the desire for the complete, nuanced experience offered by the original text․
This achievement underscores the book’s power to resonate with a wide audience, prompting reflection on legacy, oppression, and racism in North America, and solidifying its importance in contemporary Canadian literature․
The Book’s Relevance in Contemporary Society
“A Mind Spread Out on the Ground” PDF remains profoundly relevant in today’s world, as conversations surrounding social justice, decolonization, and Indigenous rights continue to gain prominence․ The book’s exploration of trauma, legacy, and systemic oppression directly addresses ongoing issues faced by Indigenous communities․
Its insights into the intersection of colonialism and mental health are particularly crucial, given the persistent disparities in mental healthcare access and outcomes․ BOOKEY offers condensed versions, but the full text provides a deeper understanding of these complex issues․
The book challenges readers to confront uncomfortable truths about historical and ongoing injustices, fostering empathy and promoting a more informed and equitable society․ It serves as a vital resource for education and advocacy․
Availability and Accessing the PDF Version
Locating the “A Mind Spread Out on the Ground” PDF requires diligent searching, as direct links aren’t consistently provided․ Various online platforms and academic databases may host the text, often requiring institutional access or purchase․ BOOKEY provides summaries as an alternative access point․

Readers can explore university libraries, digital archives, and online booksellers for potential PDF availability․ Be mindful of copyright restrictions and ensure legitimate sourcing․ The text was accessed on June 22, 2015, according to cited references․
While a free download isn’t always guaranteed, persistent searching and utilizing academic resources can yield results․ Consider supporting the author and publisher by purchasing a physical or ebook copy when possible․
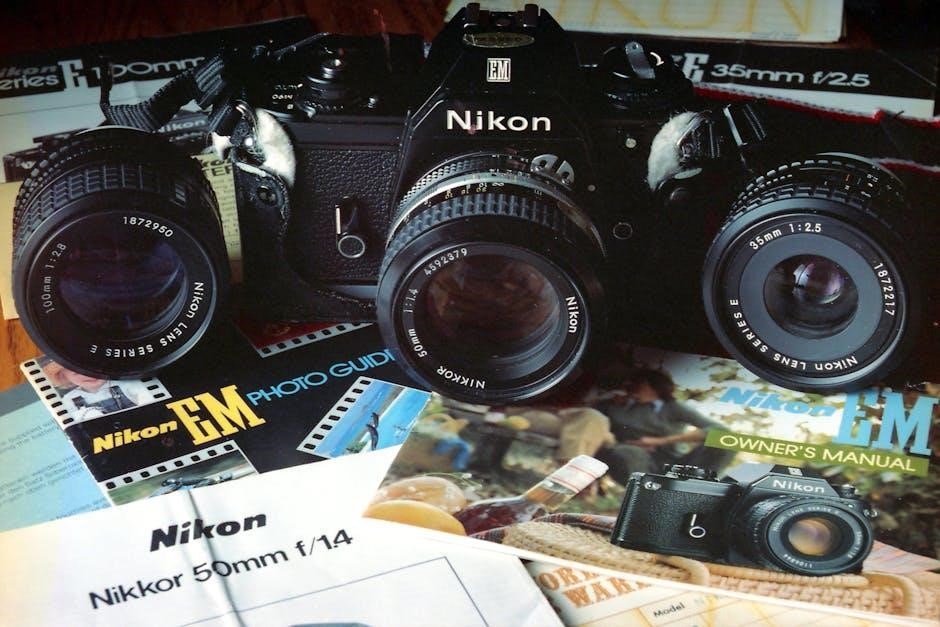
Book Summaries and Related Apps (e․g․, BOOKEY)
For those seeking a quicker understanding of “A Mind Spread Out on the Ground,” book summary apps like BOOKEY offer condensed versions of the text․ BOOKEY boasts “1000 Book Summaries to empower your mind” and “1M Quotes to motivate your soul,” providing accessible insights․
These apps are particularly useful for initial exploration or when time is limited, though they cannot replace the depth of reading the full work․ They offer a starting point for engaging with Simpson’s complex themes of colonialism, trauma, and racism․
However, remember that summaries inherently simplify nuanced arguments․ To fully appreciate the book’s artistry and intellectual weight, a direct engagement with the PDF or physical copy is highly recommended․
Academic Citations and References (Hemer, S․R․ 2018)

Scholarly engagement with “A Mind Spread Out on the Ground” necessitates proper citation and referencing․ While direct academic sources specifically analyzing Simpson’s work are emerging, related research provides contextual frameworks․
Hemer, S․R․ (2018), in “Preparing for death: Care, anticipatory grief and social death in Lihir, Papua New Guinea,” published in Mortality, 23, offers insights into the broader themes of grief, loss, and societal impact – relevant when considering Indigenous trauma explored in Simpson’s writing․
Further research will undoubtedly build upon this foundation, directly addressing the book’s unique contributions․ Proper referencing, including the PDF version’s access date (e․g․, June 22, 2015, as noted), is crucial for academic integrity and building upon existing scholarship․
Historical Context: Jefferson and Justification of Genocide
Understanding the historical roots of oppression is vital when engaging with “A Mind Spread Out on the Ground․” The text reveals a disturbing connection to past justifications for violence against Indigenous peoples․
Specifically, the book highlights how even figures like U․S; Secretary of State Thomas Jefferson adopted rationalizations – a “tantalizing, seemingly guilt-free justification for genocide” – that enabled colonial expansion and dispossession․ This historical precedent deeply informs the legacy of trauma explored within the PDF․
This context underscores the enduring impact of colonial ideologies and the systemic nature of racism, themes central to Simpson’s work and critical for a nuanced understanding of its power and relevance․
The Enduring Significance of Simpson’s Work

“A Mind Spread Out on the Ground,” whether accessed through the PDF or summarized via platforms like BOOKEY, remains a profoundly important contribution to contemporary literature and Indigenous scholarship․
Simpson’s work offers a bold meditation on trauma, legacy, oppression, and racism in North America, prompting critical reflection on the ongoing effects of colonialism․ Its national bestseller status speaks to a growing public desire to engage with these difficult truths․
The book’s enduring significance lies in its ability to challenge conventional narratives and offer a pathway towards healing and understanding, making it essential reading for anyone seeking a deeper comprehension of Indigenous experiences․